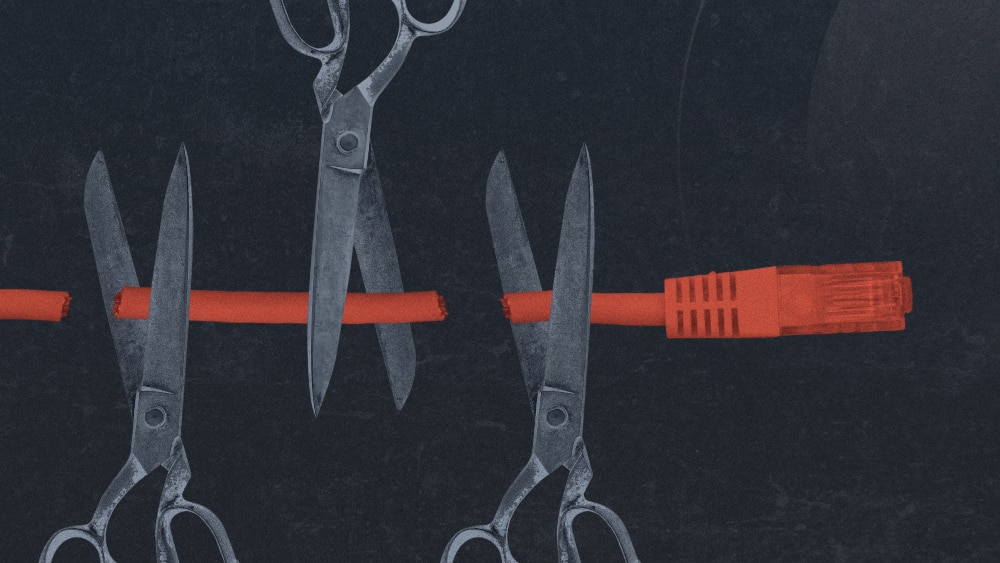
It seems like every week a new story breaks about a ransomware attack or data breach that costs an organization millions of dollars and its credibility. As applications increasingly shift towards cloud-based infrastructures, the number of successful attacks has risen. Web application attacks made up 39% of all security breaches analyzed in 2020, according to a recent Verizon study
Many of these breaches can be traced to vulnerabilities in a web application’s code that went undetected or unaddressed. As a chapter leader for the Open Web Application Security Project (OWASP), and a 20-year veteran within the AppSec industry, I’ve seen first-hand how devastating these vulnerabilities often are.
At last count, the Common Vulnerabilities and Exposures database, which serves as a repository of known vulnerabilities in open-source code, listed a staggering 186,770 vulnerabilities – and those are just the ones we know about. That’s why prioritizing and promoting application security awareness and education is crucial to a secure future. As a member of OWASP, I work every day to make sure the importance of application security is known, and that the guiding principles of AppSec are followed in the development and security communities.
About OWASP
The Open Web Application Security Project was founded over two decades ago as a non-profit foundation dedicated to promoting application security. OWASP programming and initiatives include industry-leading training sessions, educational conferences, and community-led open-source software projects. Additionally, OWASP has a physical presence around the globe, connecting AppSec professionals with more than 250 local chapters worldwide – including the London Chapter of which I have the pleasure of leading.
OWASP is the world’s premier non-profit devoted to software security, and its mission is centered on empowering developers to write better, more secure code. While OWASP creates many educational resources and hosts events around the world, it’s probably best known for the OWASP Top 10 list.
The Renowned OWASP Top 10 List
The OWASP Top 10 List identifies the ten most critical known security risks to web applications. Since its inception in 2004, the OWASP Top 10 has become the go-to document for developers to stay aware of current web and application security landscape.
Using the OWASP Top 10 to educate developers is one of the most effective first steps an organization can take to produce safer, stronger applications and software.
Although the list is published every three to four years based on consensus of AppSec experts, many of the “Top 10” most critical security risks have remained on the list for the better part of the last twenty years. In fact, on the latest OWASP Top 10, published in 2021, only three critical risks were added to the document.
4 Common Application Security Errors
Although using the OWASP Top 10 List to educate application developers, architects, managers, and organizations is a great start, more is needed to maintain a strong application security posture. Throughout my career in AppSec, I’ve noticed several common errors that many organizations are often guilty of. Left unremedied, they can lead to significant security failures.
- Relying solely on basic AppSec tools: Organizations often believe they can secure themselves by exclusively using SAST or DAST tools or Web Application Firewalls. While these tools are important, simply buying a WAF or scanning for vulnerabilities isn’t enough to stay safe. These tools can help identify weaknesses and vulnerabilities, but you must also take concrete actions to mitigate them.
- Not understanding vulnerability metrics and how to make improvements: Developers and security professionals will sometimes see a “sea of red” vulnerability scanner findings in their application’s code and not fully understand what they’re looking at. They know it’s bad but not how to fix it. The foundational understanding of vulnerability metrics and the ability to remedy security errors is a crucial part of AppSec, and one that I see missing far too often.
- Not investing in secure coding education: Web developers need to ensure they’re writing secure code in the cloud-native era, and proper training is crucial to their success. In this evolving industry, without proper secure coding training, developers won’t have the chance to improve their application security posture, which will open their code to potential vulnerabilities.
- Forgetting to make enjoyment a priority: While I’m always in favor of organizations investing in secure coding education, I know well that not all education is created equal. If you purchase and enforce mandatory classes that aren’t engaging, chances are high that your developers will click through, zone out, and not learn the critical information they need.
To make sure these security education sessions stick, it’s important to make sure the training sessions are fun and engaging. It’s best to gamify this education with Capture the Flag, “Live Hacking” events, and other hands-on, interactive approaches. We know gamification works: the University of Colorado found that “gamification resulted in 14% higher test scores for skill-based knowledge assessments.”
OWASP has several free and open-source educational games that can meet these needs, including OWASP Cornucopia, OWASP Web Goat, OWASP Juice Shop, and OWASP Security Knowledge Framework.
How to Support OWASP and Promote Application Security
Application security needs to keep pace with the rising popularity of web and mobile applications.
If you’re a developer, security professional, or someone interested in application security and the role it plays in our online world, I encourage you to check out OWASP to learn how you can become part of our community. OWASP has a global footprint of more than 250 regional chapters worldwide, so be sure to look for a chapter near you.
Finally, if you’re interested in learning more about OWASP, application security classes, or where the AppSec industry is headed in the next few years, be sure to watch my full conversation with Steve on DevSecTalks!
Did you enjoy this episode of DevSecTalks? Tune in to our other sessions to hear from more DevSec industry experts who are building the future of cloud security.