How to Build an Enterprise Data Security Team
Leading a data security company comes with great responsibility. A good chunk of my time is spent with security leaders discussing top-of-mind trends and topics.
One trend I’ve come across is the desire of security leaders to rebuild their data security teams – which also happens to raise many questions. For example: What areas should the team be responsible for? What skills and tools should they be looking for? What KPIs should they use to measure the team’s ability to support the organization’s growth in this new era?
This was also the topic of a recent talk that I, together with my good friend Tyson Kopczynski, Global CISO of Oportun, gave at the Team8 CISO summit.
Why Are Enterprises Building Dedicated Data Security Teams?
Before diving into the details, let me address a more basic question. Why are organizations rebuilding their data security teams in the first place?
The shift to cloud computing has been accompanied by new ways to process and store data. Given that microservices are now the new norm, data has sprawled and fragmented, with each team using its own copy of the data. And the end result is that organizations are now facing a number of new challenges:
More Data Collected
To support the vast amount of collected data, the size and variety of data assets in a typical organization has grown by at least 4 times, leaving it with over 20 different types of data services (i.e. storage, database, and analytic platforms) spanning hundreds – if not thousands – of instances. And the numbers keep on growing.
More Shadow Data
The result is a growing amount of “shadow data'' that accumulates in the form of orphaned snapshots and database backups. Since they can’t be tracked by legacy tools, they can be easily exposed to attackers looking to ransom data. Even if you take ransom money out of the equation, the average cost of a data breach exceeds $4 million, according to IBM’s Cost of a Data Breach 2022.
More Regulations
As data continues to move and grow, organizations are required to comply with more data privacy, data sovereignty, and data governance regulations. Keeping inventory of PII, PCI, and PHI data, however, is more challenging than ever, especially with most tools limited to a single architecture, service, cloud, or policy.
As with any new reality, there’s a need for new solutions and a new security stack. With the perimeter now irrelevant, security leaders are realizing they need to secure the data itself. In the past, protecting sensitive data from exfiltration was done either at the endpoint (EDR) or the network (NDR/XDR). But 90% of attacks on data in the cloud never even reach the endpoint.
That’s why security leaders are quickly realizing that to succeed in the new world of data, they need a dedicated data security team. But where should they begin?
Key Responsibilities of a Data Security Team
A good place to start is by defining the responsibilities of a data security team and understanding how it differs from other cybersecurity groups.
Data Inventory and Classification Across All Enterprise Datastores
There’s an old saying that you can’t protect what you don’t know. Knowing your data, where it is stored, and what is stored in it is at the top of the team’s responsibilities and represents the foundation of data security. An organization’s data assets are not stored on-prem, but rather in cloud SaaS, PaaS, and IaaS, with the latter providing no data management APIs. And more than half of cloud data is considered “dark” – that is, data no longer in use that is left unprotected.
Data Classification
Data classification identifies personal information (PII), patient records (PHI), and credit card information (PCI). But it can also locate an organization’s crown jewels such as trade secrets. Whether the data is structured, semi-structured, or unstructured, all of it should be classified. In addition, inventory should include other data contexts such as location, environment (production vs. development), or anything else that can help you decide how it should be protected.
Data Ownership and Governance
The team should engage its business units to assign data owners by providing them with context. Data owners can determine whether certain risks should be remediated or controlled. For example: Should encryption be turned on? Should versioning be conducted? Should access be granted or removed?
Data Security Posture Management (DSPM)
Your data security team should ensure that proper controls are assigned to all data assets. These include encryption, logging, retention, authentication, and authorization for datastores that contain customer and other sensitive information. Using the context of the data (through discovery) can help you prioritize various risks and work with their business owners to remediate.
Real-Time Data Detection and Response (DDR)
Since data is constantly changing, each risk that arises represents an opportunity for an attacker to exploit. No data security stack could be complete without real-time detection of risks followed by response.
Understanding the Data Attack Kill Chain
Knowing your enemy and how they act improves your chances to win. Here’s an example of a series of events that can lead to data theft and exfiltration:
- Disabling security measures or modifying IAM policies are examples of an attacker making “first moves” along the data kill chain.
- Disabling control that allows data movement across different accounts could constitute a compliance breach.
- Starting mass download of sensitive data, altering storage in production environments, or transferring sensitive data to a foreign account are examples of popular attacks that often take months to discover, especially if the attackers cover their tracks.
Applying Data Detection and Response (DDR) to All Data
The ability to detect events and respond in real time to attacks is essential regardless of where your data is stored. To carry out DDR, you need to:
- Actively monitor all sensitive data assets across different environments using available logs
- Build a threat model around the attack vector for each data service such as storage bucket, database, and data analytics to map the steps – for example, reconnaissance, first move, and attack – in the attack kill chain
- Analyze each data interaction that could lead to a breach, and when a real threat arises, immediately raise an alert to issue a response
The Data Security Toolkit
The world of information protection is complex. You can simplify current offerings by dividing them into three categories.
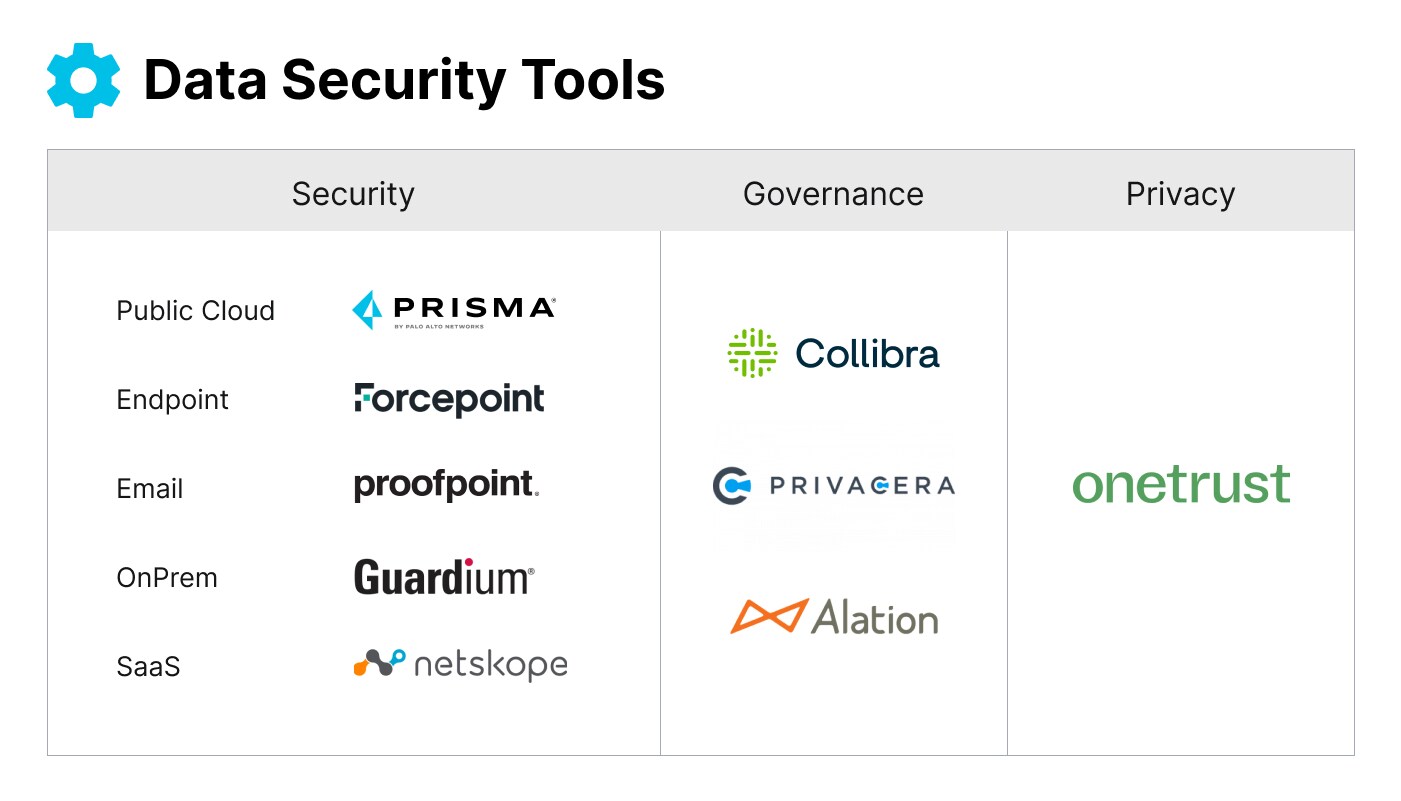
- Data privacy: Focuses on fulfilling privacy regulation requirements for data containing PII and PHI through business workflows such as data subject access rights (DSARS) and data subject consent tools. Examples include OneTrust and BigID.
- Data governance: Focuses on building policies to define who is allowed to access sensitive data through role definitions and data ownership. Examples include Colibra, Privacera, and Alation.
- Data security: Enterprise data currently resides across five locations, each with its own solution. With 60% of the world’s corporate data stored in the cloud, data security is clearly becoming the largest force in the market today.
Lessons Learned from Building a Data Security Program
Building a data security team does not happen overnight and requires an understanding of the domain and the business. Learning from others who have either built a team or experienced its establishment can help you avoid mistakes along the way. Here are a few points to keep in mind:
Accelerate Time to Value Using the Right Tools and Internal Partners
Many teams fail to estimate the total cost of building versus buying solutions, especially in cybersecurity, which involves a never-ending cat-and-mouse game. Finding the right tool for your business will save you time and money. Partner internally with people who will support your initiatives and help you drive the change you need.
Start with “The Edges”
Don’t try to build granular policies on day 1. There are problems common to all datastores, such as visibility and classification. Start by discovering where your sensitive data is and what is stored in it. This will help you prioritize your work later on by applying top-down logging and retention.
Separate Static Risk and Real-Time Risk
Different risks are remediated by different teams. Static risks, such as misconfigured data (e.g. bucket open to the world, production data not encrypted) should be handled by the data owners and IT. Real-time events that pose a risk, like an actor’s attempt at transferring data to an external account, should be handled immediately upon being alerted by the security operation team (SOC).
Additional Tips
- Train your data security analysts in mitigating data risk
- Train your SOC team in real-time data security alerts
- Hire people who can navigate the organization and understand complex environments. Borrow people from relevant teams such as GRC, IT, and IAM. Bringing about change requires an understanding of the existing processes and working with familiar colleagues to help drive and support it.
- Focus on where data is growing at accelerated rates. That’s where new attacks will be coming from.
Measuring Success from Inception to Launch
As you’re building your data security team, consider who you should be adding. To measure their success once a program is up and running, take a look at the questions below. How you answer them is an excellent way to track your KPIs.
- What data does my organization collect and store?
- Can I list all locations where sensitive data resides? Do I know what type of sensitive data exists in each location?
- Do we have data owners assigned for different data stores, and do they certify the data controls periodically? Who can access sensitive data, and what are they allowed to do with it?
- How do we strengthen the security posture of all sensitive data such as encryption, logging, and retention, which, unless remediated, may lead to data leaks?
- Do we monitor our data assets to identify suspicious activities that may lead to data exfiltration?
- Data detection and response (DDR) and cloud data loss prevention (DLP) – Do we have the right controls to detect and stop data from exfiltrating from our organization?
- Can we respond to new data risks within minutes to stop data leaking and prevent a breach?
- What are our company’s data security policies, and how often are they updated? What compliance requirements apply to my organizations, and are we aligned with our internal and external auditors?
- Are we using tools to defend our organizational data from recent attack techniques (tools that use frameworks such as MITRE and are up to date with current adversary tactics)?
Learn More
If you’re interested in discussing this with me, please get in touch. I’d love to support your journey of building an enterprise data security team. And if you’d like to see Prisma Cloud in action, why not book a demo?
Related Blogs
Subscribe to Cloud Native Security Blogs!
By submitting this form, you agree to our Terms of Use and acknowledge our Privacy Statement. Please look for a confirmation email from us. If you don't receive it in the next 10 minutes, please check your spam folder.