Phishing Response Remains Critical
Phishing is involved in almost 40% of security incidents, according to the 2022 Unit 42 Incident Response Threat Report. Attacks that once relied on poorly written phishing emails to find victims have rapidly increased in sophistication and targeting due to the growing amount of personal information easily found on the internet.
SOC analysts might encounter many types of phishing attacks daily, from opportunistic campaigns to spear phishing, including attachments or just probing for more information. Attackers use phishing techniques to deliver malicious payloads or harvest information for sale or future use. Since phishing email deployment only requires the click of a button, the sheer volume of emails to analyze can be overwhelming and quickly consume SOC resources. If we know analysts are faced with these threats, we need to equip them with the proper tools.
With Cortex XSOAR, phishing responses can easily be automated and it is one of the most popular use cases for automation.
The Cortex XSOAR Phishing Pack
The Phishing pack helps organizations reduce the time spent managing phishing alerts and provides a standardized, methodical process to handle phishing. The main playbook helps to:
- Facilitate analyst investigation by automating phishing alert response and custom phishing incident fields, views, and layouts.
- Orchestrate across multiple products, including cross-referencing against external threat databases.
The pack also leverages machine learning to intelligently identify phishing campaigns targeting multiple users in the organization, linking them together and allowing full interaction and control over the campaign from within the incident layout.
How Does It Work?
The phishing content pack helps automate phishing response via the following steps:
- Retrieves emails from user inboxes or ingests them using mail listeners
- Creates a phishing incident within Cortex XSOAR
- Extracts and enriches indicators from email attachments
- Analyzes files and provides reputation using available sandbox and threat intelligence integrations
- Generates a screenshot of the email and embedded links and calculates reputation for all indicators involved
- Runs checks for SSL certificates of URLs, email address breach involvement, domain-squatting, and email authenticity using SPF, DKIM, and DMARC checks
- Identifies similar phishing incidents of the same campaign, providing visibility and manual or automatic actions to respond
- Calculates severity for the incident based on the provided initial severity, indicator reputations, email authenticity check, and critical assets
- Remediates the incident by blocking malicious indicators and searching for and deleting malicious emails upon analyst approval
- Engages with the end user regarding the incident, such as notifying them of receipt of the email and providing further instructions if an email is found to be malicious
As part of this pack, you will also get out-of-the-box phishing incident views, a full layout, and automation scripts. These are all easily customizable to suit the needs of your organization.
What Is the Deployment Wizard?
Cortex XSOAR introduced the use case deployment wizard to ease the integration process and playbook parameter configurations (about the wizard). The deployment wizard was introduced earlier this year to help customers adopt automation from the XSOAR marketplace faster and more efficiently. The wizard has three main phases:
- Configuring ingestion of the alerts (phishing emails)
- Configuring the main playbook
- Configuring any supporting integrations
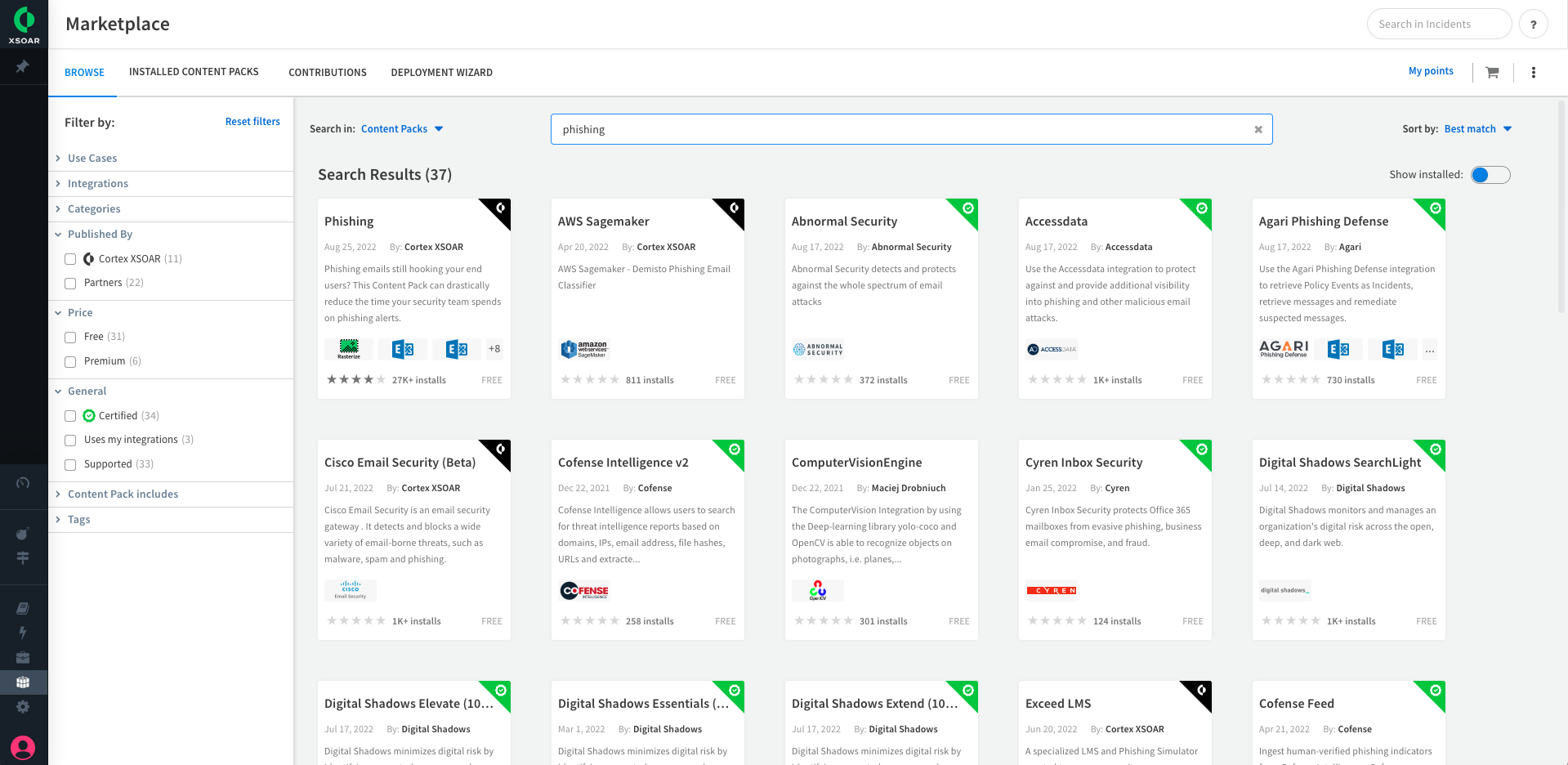
Let’s Fish for Phishing
- Select the Phishing pack from the Marketplace.
2. Select the Email Gateway to use and support integrations.
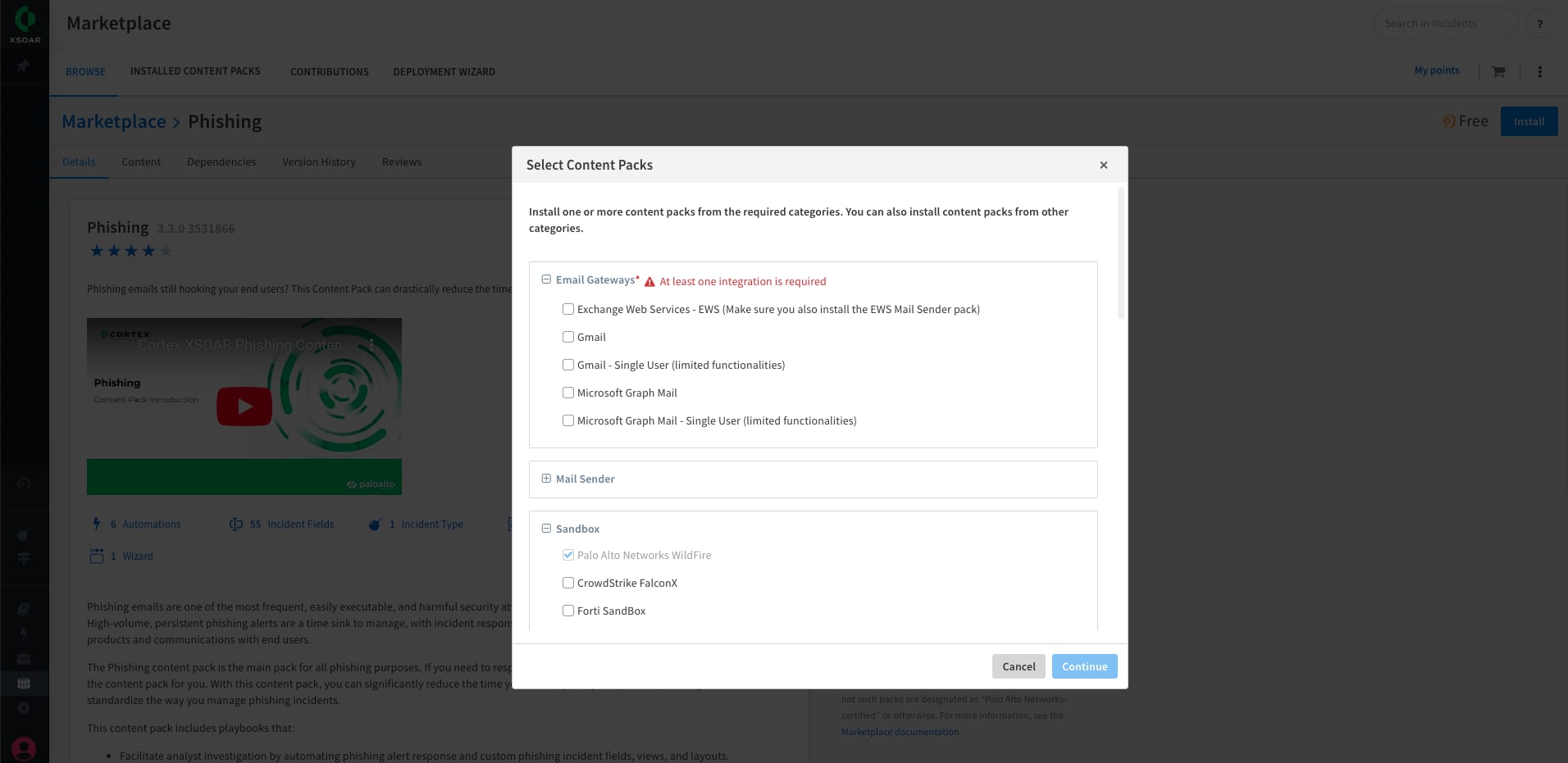
3. Install the packs that were added to the cart
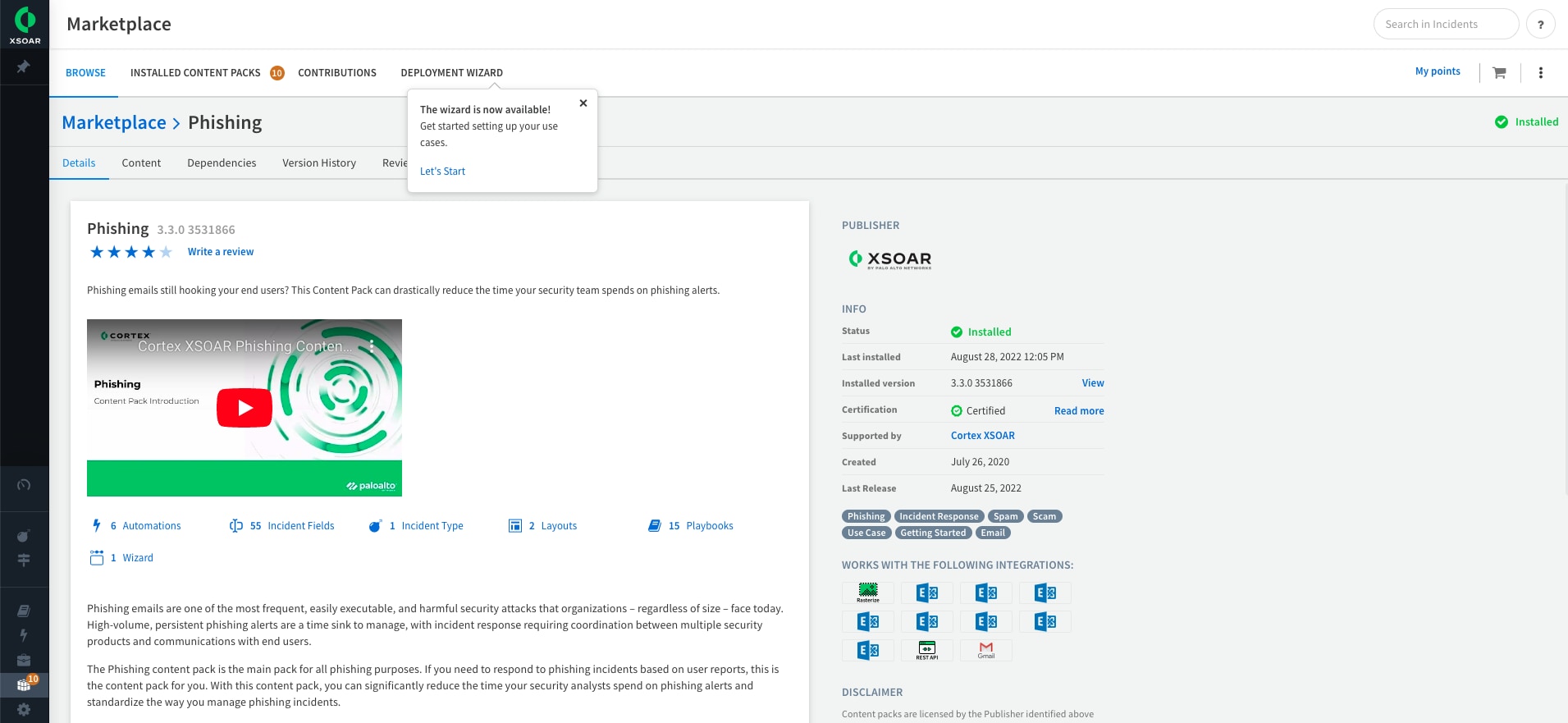
4. Subscribe to the pack (from version 6.8)
5. Enter the phishing Wizard Process
6. Configure fetching integration and set fetch configuration to true to enable automatic retrieval of emails
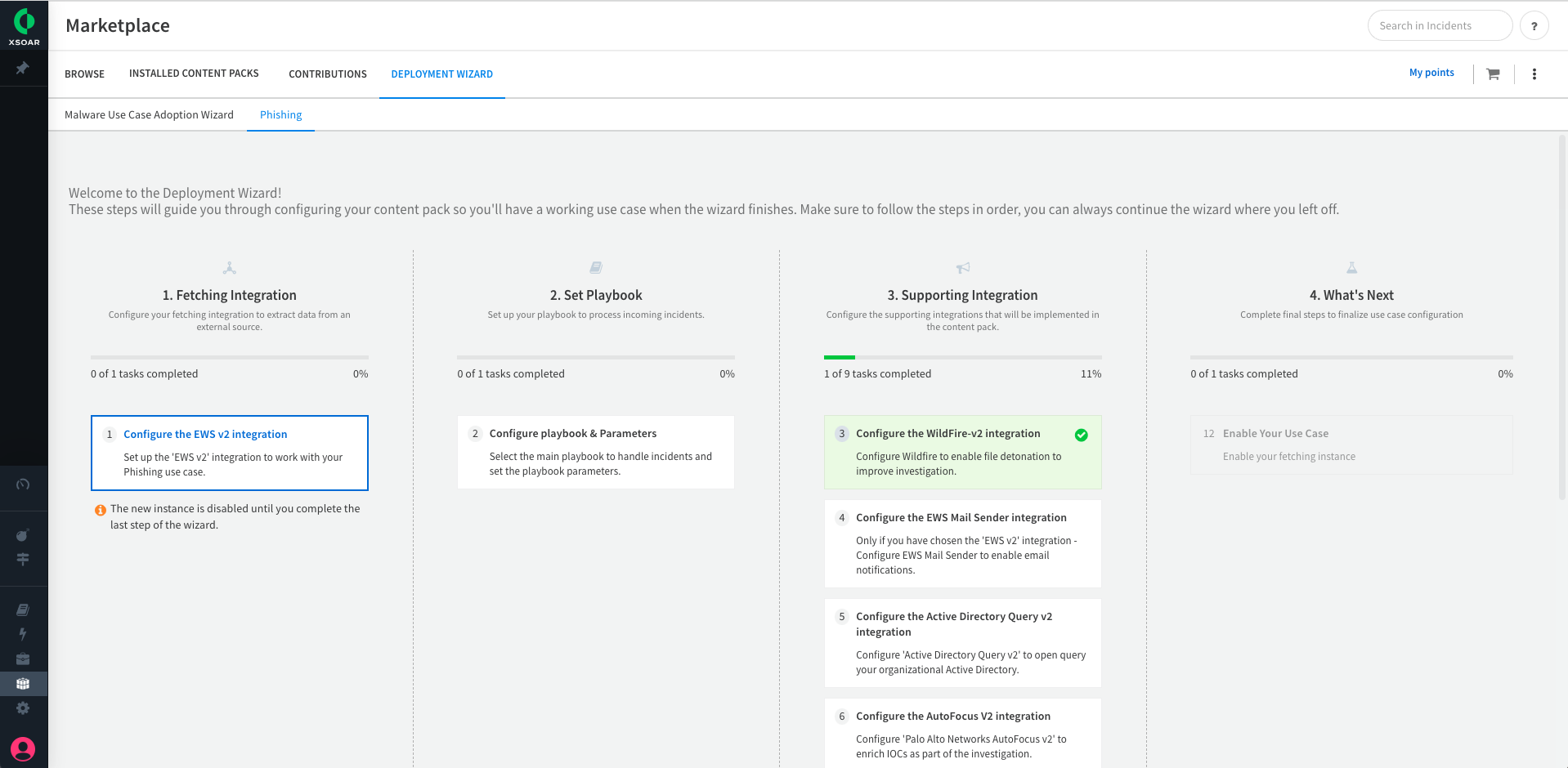
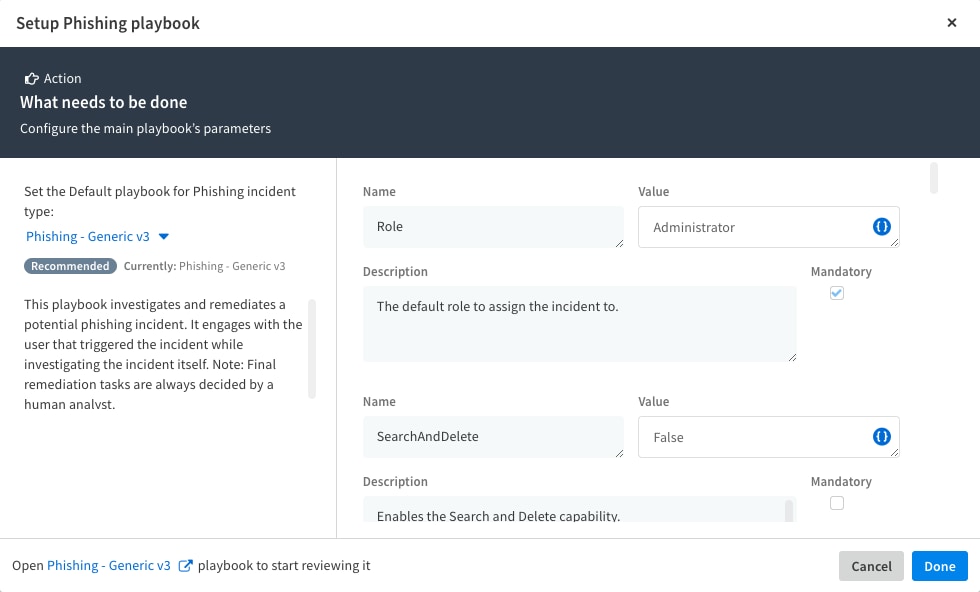
7. Set Playbook Parameters according to the organization’s preferences. These can be reconfigured in later stages.
8. Configure supporting integrations, preconfigured integrations will be marked in green.
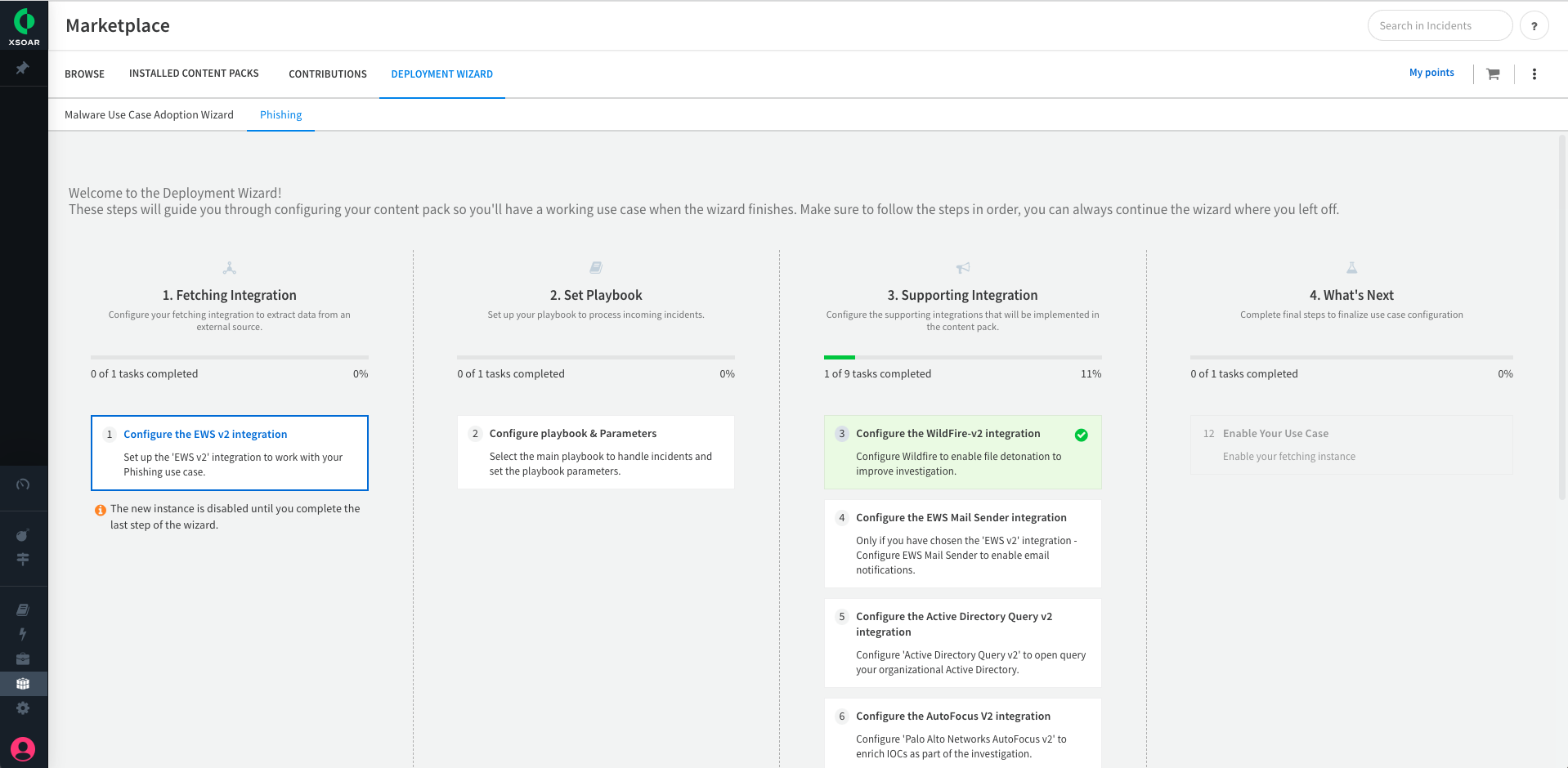
9. Validate that everything is configured and turn on your use case by enabling fetching source in step 4.
10. Stop Phishing!
For more information on the Cortex XSOAR Phishing pack, including a quick demo, visit the Phishing page on the Cortex Marketplace. If you need to respond to phishing alerts ingested from email gateway integrations, check out the Phishing Alerts content pack (Phishing content pack required).
To learn more about how you can automate security operations with Cortex XSOAR, check out our virtual self-guided XSOAR Product Tour
We also host virtual and in-person events, so check here for upcoming ones.