RANSOMWARE PROTECTION
Defeating ransomware requires advanced, proactive AI-powered security, automated across your network and endpoints.
Traditional network and endpoint security simply haven’t kept up with rapidly evolving threats. Relying on outdated antivirus signatures won’t help you block new and evasive ransomware.
Attackers today leverage sophisticated evasion techniques like running in memory and loading malware from virtual machines to bypass endpoint defenses.
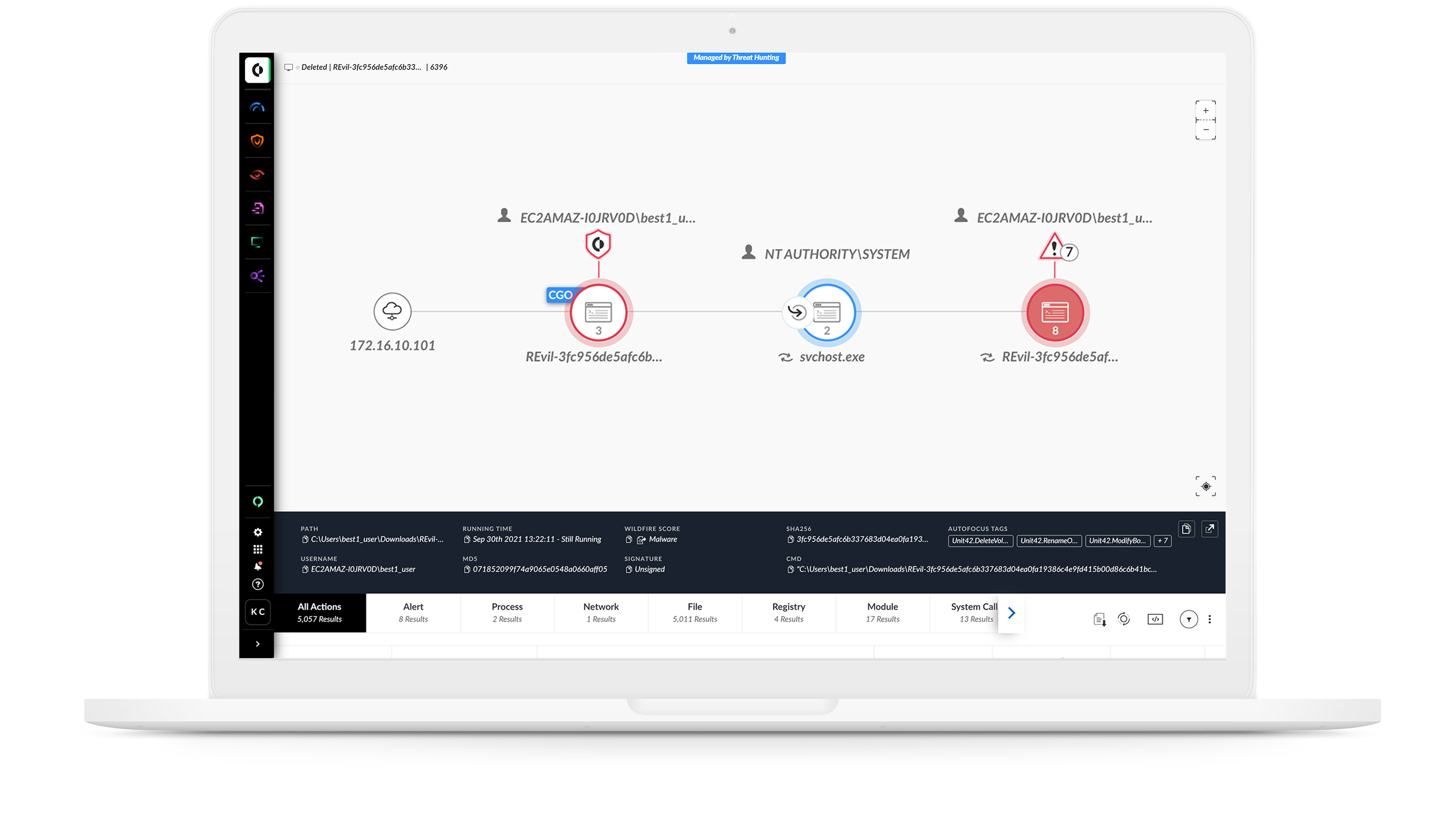
Ryuk, WastedLocker, REvil and other ransomware use targeted attack techniques and worm-like capabilities to swiftly infect hosts. You must block every step of an attack, from delivery to hard-to-detect lateral movement, and then quickly restore compromised hosts if needed.

INTELLIGENT & SECURE
Defeat ransomware with machine learning
Inline analysis stops exploits that lead to infection, and always-up-to-date machine learning models monitor behavior to pre-emptively stop unknown and zero-day threats, including ransomware.
CORTEX XDR
Cortex XSOAR
WildFire
NGFW
CONSISTENT & AUTOMATED
Stop threats instantly in all locations
Cortex XSOAR
CORTEX XDR
WildFire
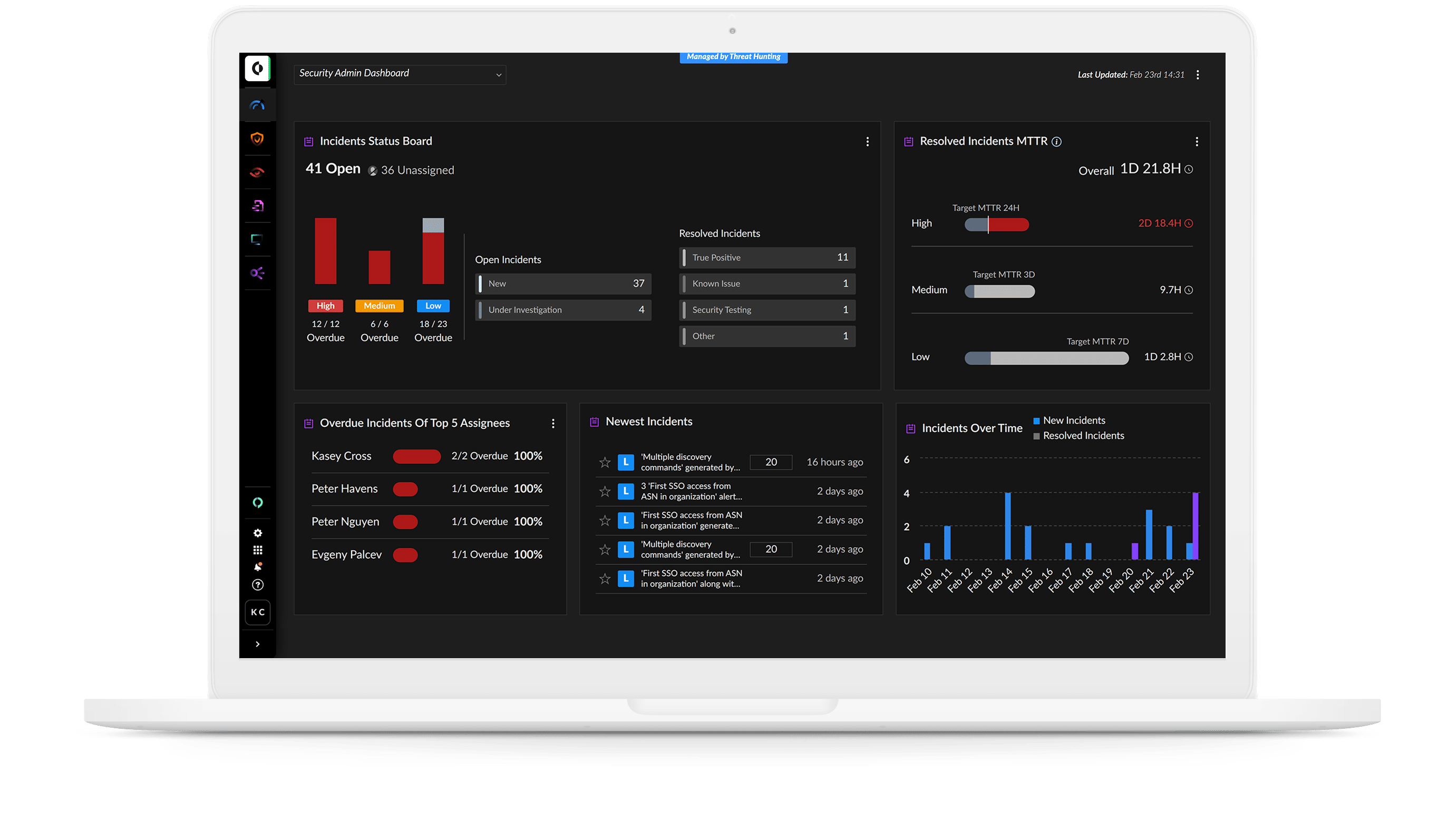
Call in the special forces
When attackers strike, security teams must act quickly and efficiently. Automated playbooks ensure mitigation steps are taken, buying time to coordinate a response. When needed, our incident response teams deploy faster, hunt smarter, investigate deeper and contain completely, so you can limit your damages and get back to business.
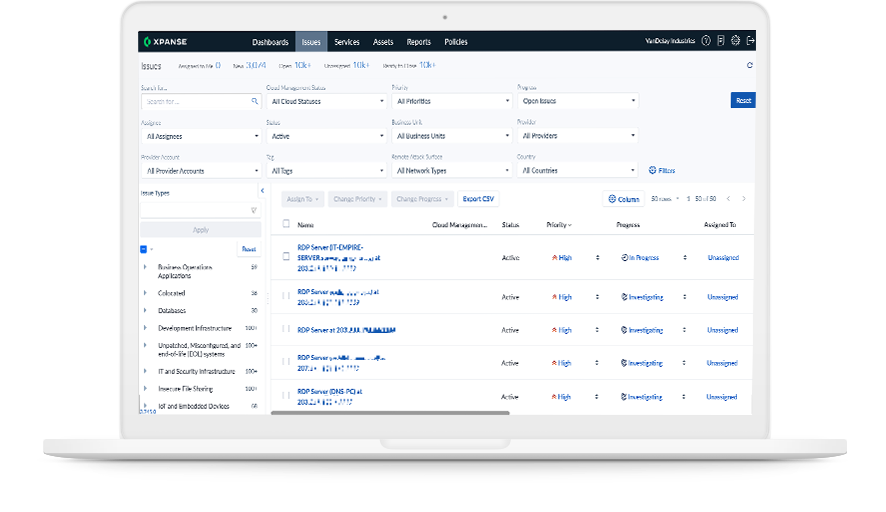
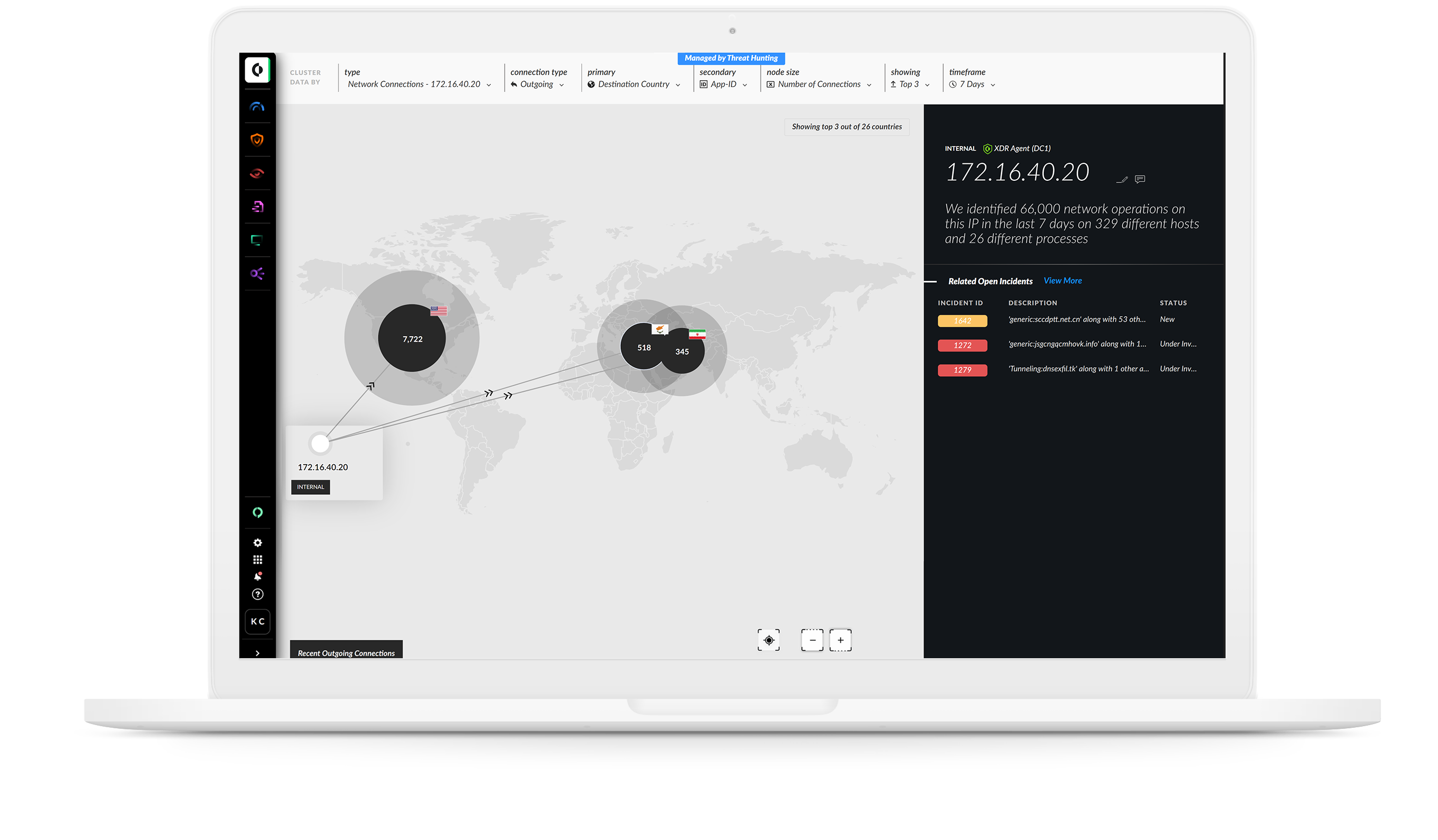
Find exposures before they become attack vectors
Discover exposed remote access ports
Find unknown assets and risks
Continuously monitor your attack surface
Feed data to your SOAR
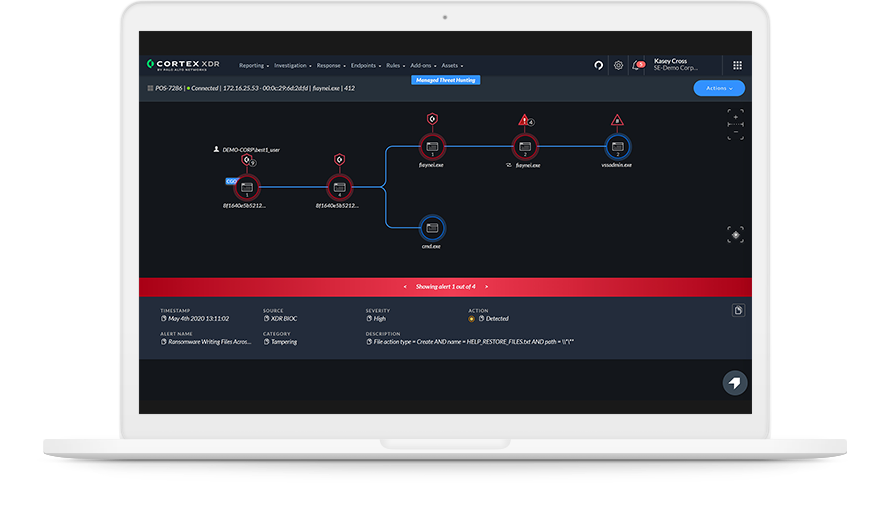
Prevent ransomware with industry-best NGAV
AI-driven local analysis to stop zero-day threats
Comprehensive exploit prevention
Anti-ransomware protection for behavioral analysis
Device control, disk encryption and firewall
Holistic endpoint, network and cloud protection
Simplified operations with cloud deployment
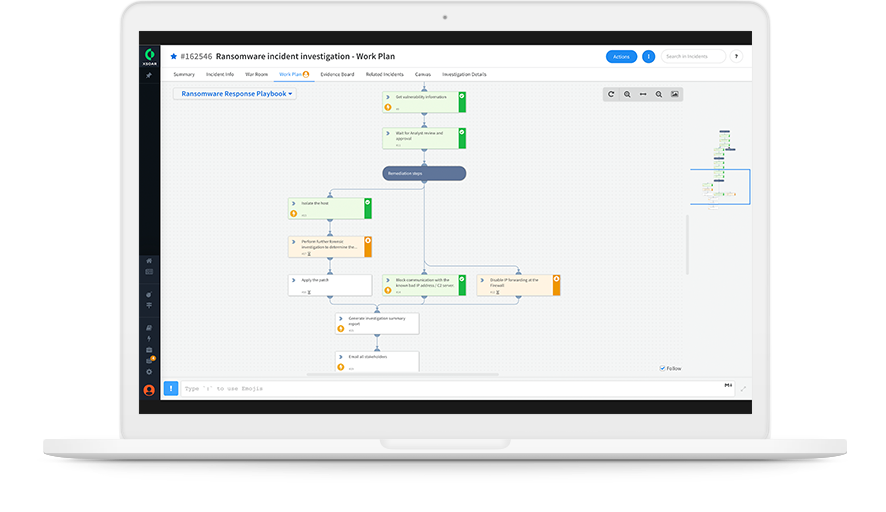
Post-intrusion ransomware investigation
Automated user data enrichment
Automated host data enrichment
Indicator extraction and blocking
Automated user and endpoint isolation
Guidance on additional remediation

Expert incident response
Rapid deployment
Deep investigations
Complete containment
Recovery plan development
Minimized cost and downtime
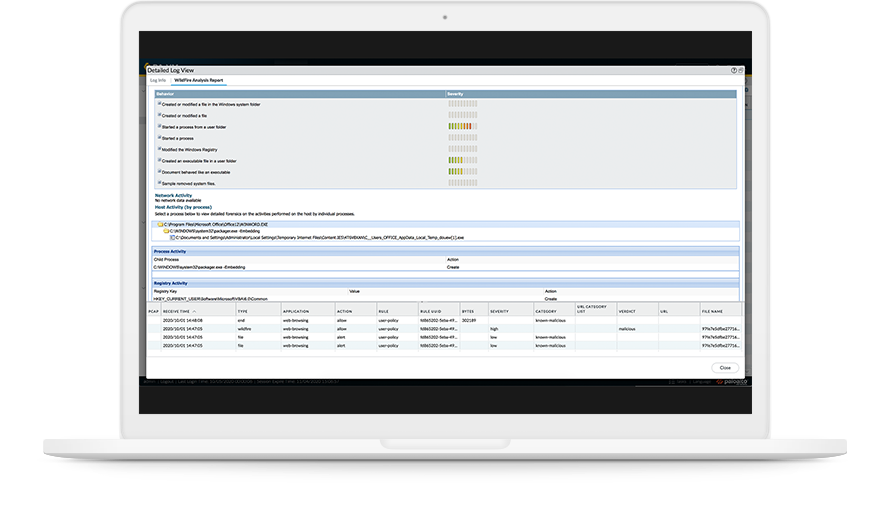
Eliminate risk from highly evasive malware
Inline machine learning
Real-time protections
Unknown threat prevention
Instant intelligence sharing
Dwell time elimination
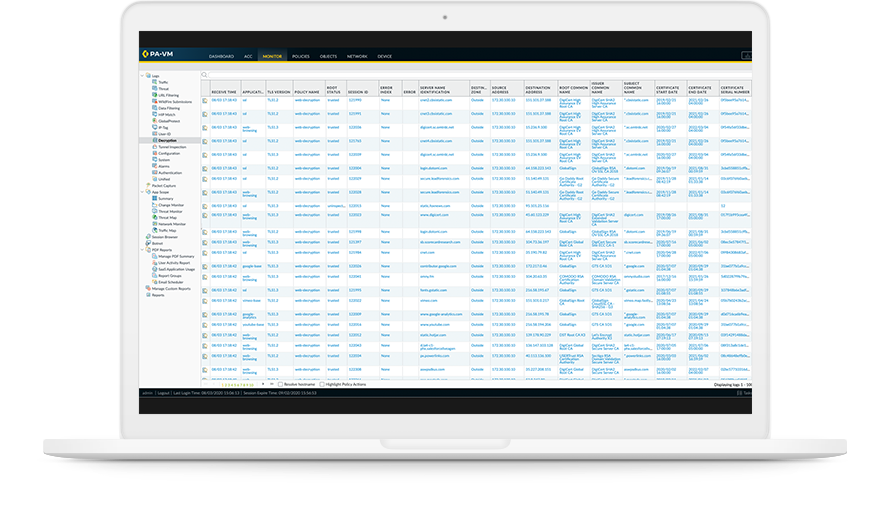
Eliminate risk from highly evasive malware
Inline-ML threat prevention
Advanced threat blocking
Automated network security
Flexible deployment options

