Accelerated digital transformation has made it difficult for your security operations center (SOC) and application security (AppSec) teams to keep tabs on your external web attack surface. Your web attack surface spans everything from a single source of truth for your web inventory to being able to monitor software supply chain risks due to third-party technologies or dependencies attributed to an organization’s web artifacts.
Lack of visibility into these dependencies and their outdated artifacts creates serious cracks in your web attack surface, putting your organization and customers at risk. Unpatched vulnerabilities continue to wreak havoc for security teams. Recently, attackers targeted 30 vulnerable WordPress plugins 1 that were supporting thousands of websites.
With WordPress sites being constantly created and abandoned by their owners, it leaves them open to exploitation by bad actors. Organizations tend to have abandoned sites that were created for one-time events, or by an employee that has left the company. These websites go undetected and create cracks in your security posture. Beyond websites, this could also happen with code repositories, web directories, and much more. Without complete, current, and accurate visibility, it’s difficult to manage these website assets when you don’t even know what’s yours.
Cortex Xpanse is an active attack surface management solution that helps your organization actively discover, learn about, and respond to unknown risks in all connected systems and exposed services. Through consistent indexing and high fidelity attribution, we help our customers identify what assets belong to them and often find they own 20-30%2 more internet-facing assets than they had been tracking.
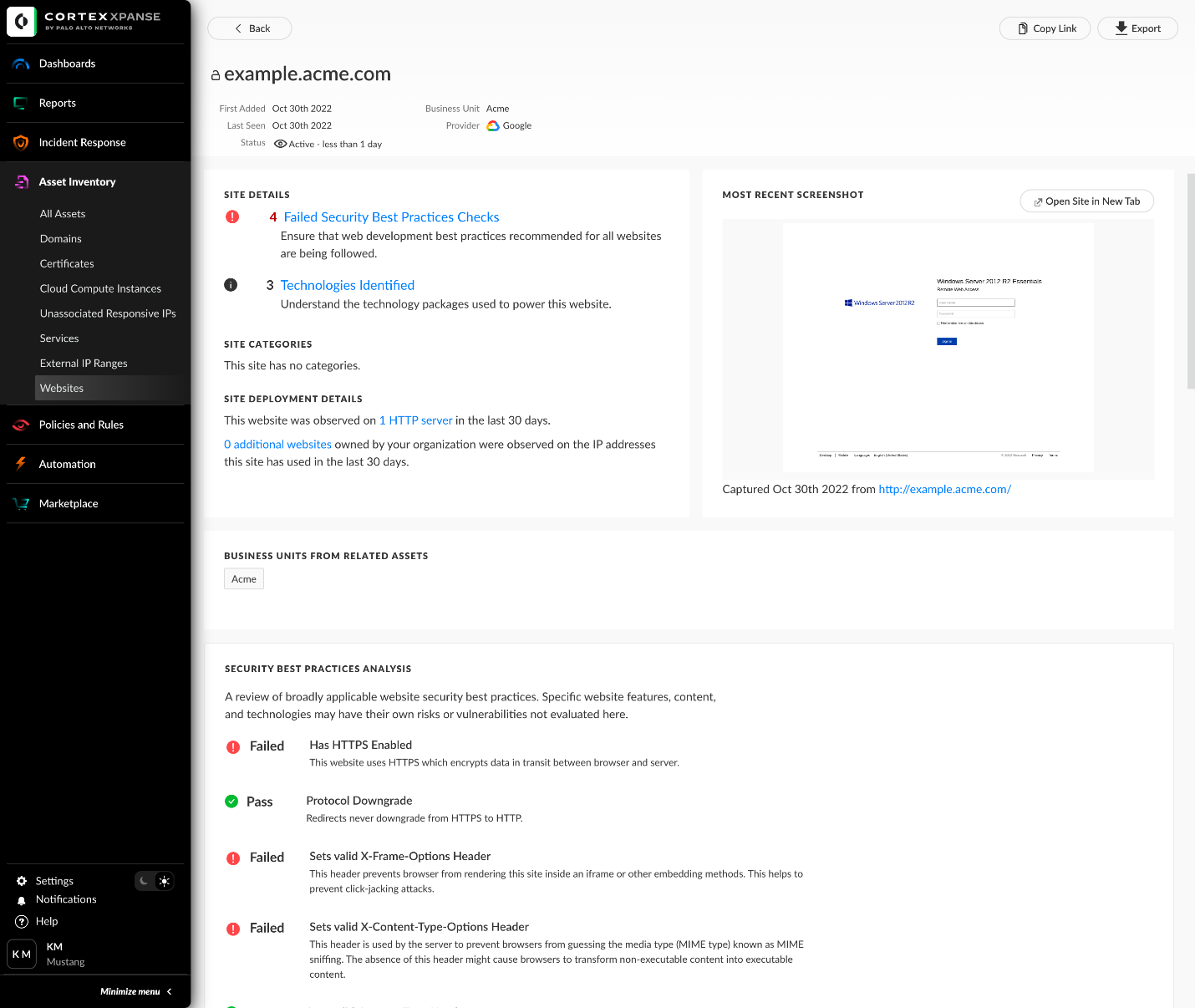
Your security teams can use our new Web Attack Surface Management (ASM) feature to get complete, current, and accurate visibility into your public-facing web infrastructure without any manual work. Automatically get visibility, including your exposures to WordPress plugins, some of which might be among the 30 unpatched vulnerabilities published this week. Additionally, your teams can use Web ASM capabilities from Cortex Xpanse to:
- Continuously discover and monitor your website inventory and web technologies.
- Identify insecure and misconfigured websites in your environment.
- Identify sites failing security best practices and putting users at risk.
- Track and measure the risk due to third-party libraries or dependencies attributed to an organization’s web artifacts.
- Identify websites serving sensitive content such as personally identifiable information (PII) and payment forms using insecure protocols.
Attackers are only becoming more sophisticated and new vulnerabilities are emerging daily. Some of the world’s largest and most demanding organizations use Xpanse to secure their attack surface by reducing their risky exposures. Xpanse protects the U.S. Department of Defense, all six branches of the U.S. military, several federal agencies, and large enterprises like Accenture, AT&T, American Express, AIG, Pfizer, and over 200 others.
To learn more, join the Xpanse product team for a discussion and demo of these new capabilities. Register for the “Active Attack Surface Management with Cortex Xpanse” webinar to save your spot!
1 Arstechnica: Hundreds of WordPress sites infected by recently discovered backdoor
22022 Cortex Xpanse Attack Surface Threat Report, Palo Alto Networks, April 19, 2022.